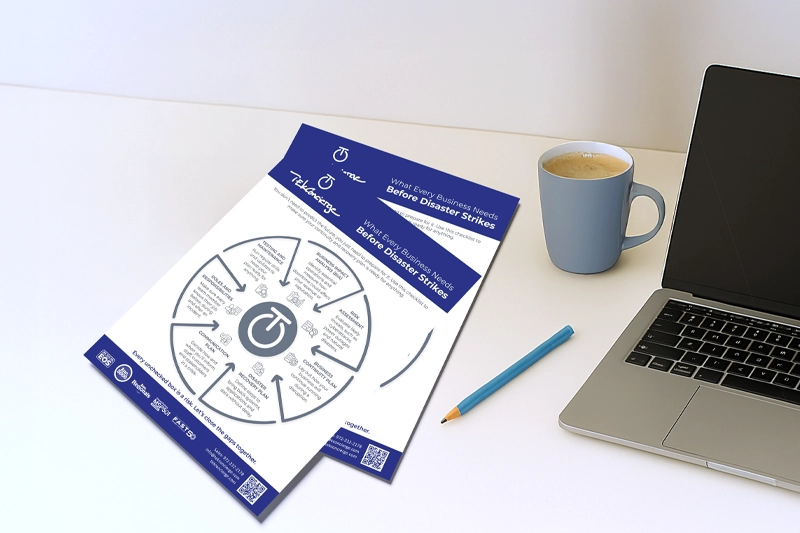
Beyond the Breach: Incidence Response Checklist
Safeguarding Your Digital Fortress: A Comprehensive Incident Response Guide
Digital threats are intensifying daily, making a robust incident response plan more crucial than ever. Sophisticated adversaries evolve, leveraging new strategies and technologies to penetrate defenses. In this battle, preparation transcends mere helpfulness to become your paramount defense. Let’s explore how to bolster your organization’s defenses against these relentless threats.
Preparation: Your Defense Foundation
The first, and perhaps most crucial, phase in incident response is preparation. This involves several key steps:
- Identify Critical Assets: Understand what data, systems, or components are vital to your organization’s operations. Knowing what’s most important helps prioritize efforts and resources.
- Create a Documented Response Policy: Having a well-documented incident response policy ensures a quick, organized, and effective reaction to incidents. This policy should outline procedures, roles, and responsibilities.
- Employee Awareness: Every member of your organization plays a role in its security. Ensure all employees are aware of their responsibilities in defending against and responding to incidents. Regular training and drills can help reinforce this knowledge.
Detection and Identification: Your Early Warning System
Continuous monitoring of your infrastructure is vital. The earlier a threat is detected, the less damage it can do. This phase focuses on:
- Implementing Advanced Monitoring Tools: Use sophisticated software to keep an eye on your systems for any signs of unauthorized access or suspicious activity.
- Threat Hunting: Proactively search for threats that may have bypassed initial defenses. This active approach helps uncover hidden threats.
Containment, Eradication, and Recovery: Eliminate and Restore
Once a threat is identified, immediate action can prevent further damage:
- Containment: Isolate affected systems to stop the spread of the threat. This might involve disconnecting infected devices or restricting access to compromised areas.
- Eradication: Identify and eliminate the root cause of the incident. This step often requires detailed analysis to ensure no remnants of the threat remain.
- Recovery: Restore affected systems and data to their normal state. This process must be handled carefully to prevent reintroducing the threat.
Post-Incident Analysis: Learning from the Experience
After addressing the immediate threat, it’s crucial to reflect on the incident:
- Document Everything: Keep detailed records of the incident, including how it was detected, contained, and eradicated. This documentation is invaluable for the next step.
- Lessons Learned: Review the incident to identify any weaknesses in your defenses and response. What worked well, and what could be improved?
Continual Improvement: Evolving Your Defenses
Threat landscapes change rapidly, and so should your incident response plan. Regularly revisiting and updating your plan ensures it remains effective against new threats. This phase includes:
- Testing and Drills: Regularly test your plan through drills and simulations. This helps identify gaps and areas for improvement.
- Staying Informed: Keep abreast of the latest security trends, threats, and best practices. This knowledge can help you anticipate and prepare for future threats.
By following these guidelines, you can create a dynamic and resilient incident response plan capable of defending your organization against sophisticated digital threats. Remember, in the digital realm, preparation and adaptability are your best allies.