TekConcierge Named to Inc. Regionals’s 2026 List of the Fastest Growing Private Companies in the Southwest
Companies on the Inc. Regionals Southwest list had a median growth rate of 79 percent. Dallas, TX, March 31, 2026 Inc., the leading media brand and playbook for the entrepreneurs and business leaders shaping our future, today revealed that TekConcierge has been ranked No. 81 on its sixth annual Inc. Regionals Southwest list, the most prestigious ranking of the fastest growing
The Infrastructure Behind Hotel Connectivity: A Look at HTS’s 2025 Impact
Reliable connectivity has become a foundational part of the modern hotel experience. Guests expect seamless WiFi whether they are working from their rooms, attending conferences, or relaxing in public spaces throughout the property. Delivering that level of performance requires extensive planning, installation, and infrastructure that often goes unnoticed by the end user. Our partner, Hospitality Technical Services (HTS), recently shared a
AI Without a Plan Is a Risk. AI With a Strategy Is a Business Advantage.
Artificial Intelligence is already embedded in the tools many organizations use every day. When applied thoughtfully, AI can improve efficiency, reduce manual work, and help teams make faster, more informed decisions. The challenge is knowing where AI truly adds value—and how to deploy it safely. Without a clear strategy, organizations risk exposing sensitive data, duplicating tools, and seeing low adoption. AI
TekConcierge Wins Southwest Category at 2025 MSP Titans of the Industry Awards
TekConcierge is proud to announce that we have been named the Winner of the Southwest Category at the 2025 MSP Titans of the Industry Awards. This recognition celebrates outstanding leadership, innovation, and excellence among Managed Service Providers. For our team, it serves as a meaningful capstone to a year defined by remarkable growth and achievement. CEO Heath Carter accepted the award
Celebrating a Major Achievement Heath Carter Named a 2025 MSP Titans Finalist
We are proud to share an exciting accomplishment for our team. TekConcierge President and CEO, Heath Carter, has been recognized as a 2025 MSP Titans of the Industry Finalist in two distinguished categories: Advanced Cybersecurity and Southwest Region Leadership. These honors reflect the strength of our service, our commitment to our clients, and the leadership that continues to drive TekConcierge forward. Finalist
Your Cyber Safe Holiday Shopping Guide
Holiday shopping season arrives with great deals, fast shipping, and endless opportunities to buy gifts online. It also attracts cybercriminals who wait for busy shoppers to let their guard down. A few simple precautions can help keep your information safe while you enjoy your holiday shopping. Below is a clear guide that expands on the key security steps every shopper should
The Cybersecurity Extinction: Will Your Business Survive the Next Digital Meteor?
Millions of years ago, dinosaurs ruled the Earth. They were massive, dominant, and seemingly unstoppable. But one day, a meteor struck, and their reign ended in an instant. Fast forward to today, and businesses face their own version of extinction-level events. AI-driven cyberattacks, sophisticated supply chain breaches, and deepfake-powered scams strike without warning, capable of erasing years of progress overnight. If the
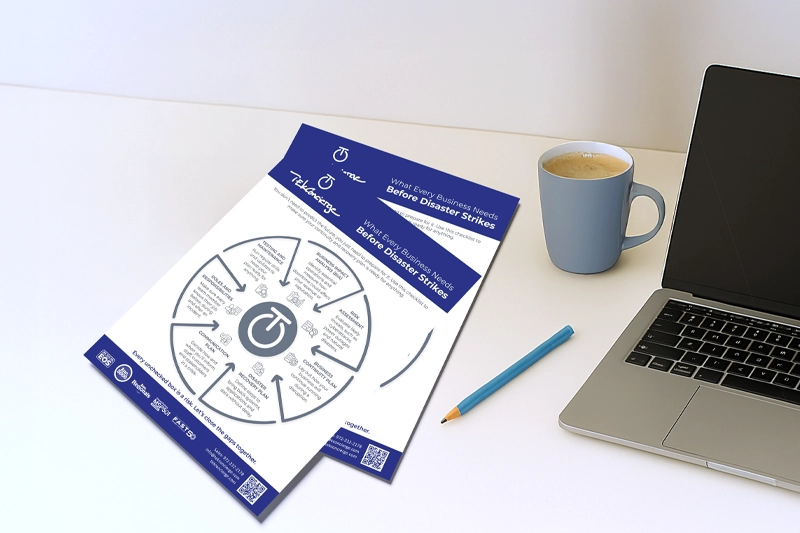
What Every Business Needs Before Disaster Strikes
You don’t need a crystal ball to know that disruptions will happen. You just need a plan to deal with them. Whether it’s a cyberattack, a power outage, or a natural disaster, the businesses that survive are the ones that prepare. Use this checklist to see if your continuity and recovery strategy is truly ready. Business Impact Analysis (BIA) A BIA helps